Fortinet security tools have proven to protect both corporate networks (including the private cloud) and the virtual infrastructure of cloud providers, replacing several devices with one function. The presence of the FSTEC certificate allows you to organize work with personal data. In this review, we will figure out and discuss all the strengths and weaknesses of the Fortinet solutions.
What Is Fortinet?
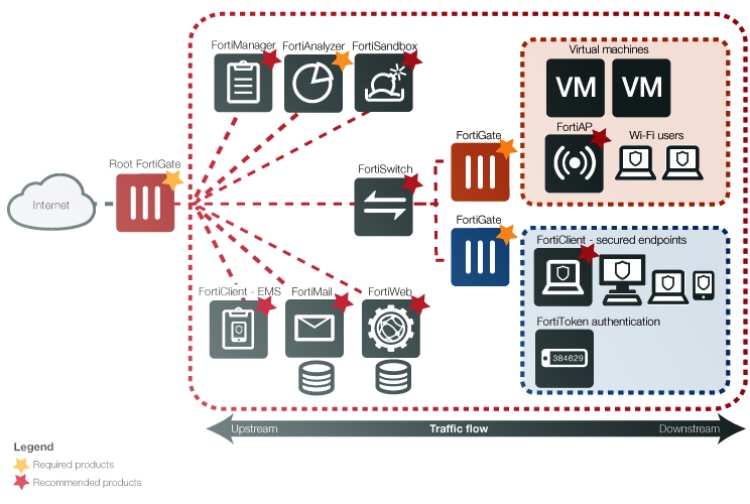
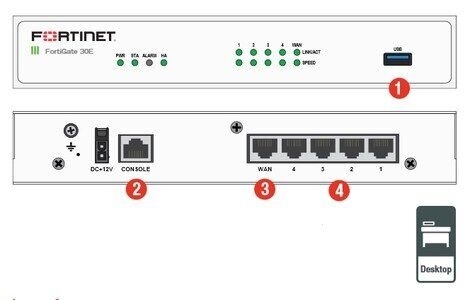
Fortinet is one of the leading manufacturers of network security devices and a market leader in integrated security devices. Fortinet high-level integrated systems are mainly used in the corporate segment of the market for an easy, fast, and efficient solution for network security systems. UTM, which is Fortinet’s main product, is multifunctional software and hardware systems that combine the functions of the following devices: firewall, intrusion detection and prevention systems (IDS/IPS), and antivirus gateway functions (FortiGate). Such complexes also have protection against unsafe websites and spam. In addition to UTM solutions, Fortinet offers a wide range of systems for ensuring the information safety of any company: from the protection of workstations to comprehensive protection of the entire company information infrastructure.
Each FortiGate review speaks about a distinctive feature of the solutions offered by Fortinet company is the use of its hardware and software solutions that are tailored for protection tasks. Such solutions include specialized FortiASIC processors designed for signature analysis of traffic and accelerate its processing and encryption. To get and manage all protection components, the FortiOS operating system has been developed. Thanks to this, Fortinet products provide real-time threat detection and elimination without loss of network bandwidth. Also, it offers a large set of tools for analyzing and managing traffic. Another business card of the company is constantly updated antivirus databases, configure security policies for the entire network using a single intuitive application, and flexible scalability of devices. It allows you to “assemble” solutions for specific tasks of a particular consumer. All these features make Fortinet products not only practical but also cost-effective.

Fortinet Pros and Cons
Regarding the specifics of the Fortinet products, they have a lot of pros, especially in the company safety field.
- Variety of security solutions (it is possible to get all the necessary tools from one supplier)
- Comprehensive approach (the company developed many protection means)
- Corporate options for businesses
- Management and sharing of configurations of local and remote points and switches
- Access configuration and authorization method for SSID or VLAN (captive portal support)
- High level of WiFi protection
- Support for various wireless technologies
- Most of the solutions do not suit personal use
- Some of the products need additional hardware to ensure seamless functionality
Fortinet Highlights
FortiOS simplifies SS deployment for mobile users and work well on the new mobile OS. Special FortiClient Endpoint Security software offers enhanced protection for devices running Mac OS, Windows 10. It is able to load security settings into user programs, including antivirus configuration, network filtering, firewall, and VPN. It also supports client software for protecting mobile devices based on Android and iOS.
The broad functionality of Fortinet firewalls gives large and medium-sized companies great opportunities for managing threats. They ensure network security and build a private cloud, and cloud providers – reliable protection of the client’s virtual infrastructure (IaaS). A Fortinet device can replace several from other manufacturers. The full control over all infrastructure elements (including IoT devices, access points, data centers, clouds, applications, and even the data itself) allows administrators to effectively manage the safety of on-premises and cloud environments, such as a secure virtual Datacenter.
However, the list of possible users of this solution is not limited to commercial organizations. With its FSTEC certificate, state, and municipal organizations working with confidential information can benefit from Fortinet products.gf rolex datejust ladies rolex calibre 2836 2813 m126284rbr 0012 range of designs to meet the requirements diverse character. cheap disposable vape represents distinctive concept of minimalism.
Features of Fortinet
Firewall
The main task of a FortiOS firewall is to control any traffic on the network by analyzing packets and issuing permission / deny according to a set of specific rules.
The Fortinet VPN
This solution allows companies to implement an encrypted connection and protect the transmission of information between several networks and hosts using IPsec and SSL VPN protocols. Also, there is support for other VPN technologies. The potential of both VPN services is increased through the use of unique FortiASIC processors, which accelerate the encryption and decryption of network traffic.
FortiOS Intrusion Prevention System

Reviews state that it can offer a large list of functions useful for monitoring and blocking unfair network activity, including default and configured signatures, protocol decryption, control rule via an auxiliary channel (IPS one-handed mode), packet logging and IPS sensors. FortiGate feature guarantees a single set of tools with a comfortable installation and configuration.
Program control
Application control is indispensable, especially for managing a large number of new Internet technologies that have flooded modern networks.
Antivirus
Fortinet antivirus concepts work with identifier-based virus detection method and a heuristic method. It provides multi-level real-time protection against both old and newest viruses, spyware, as well as other types of attacks by penetrating through Internet traffic, email, and file sharing. Monitoring anonymous and targeted attacks is possible by transferring (injecting) dangerous files to cloud or server systems for checking unknown suspicious objects.
Web filtering
Apart from the standard URL blocking lists, FortiOS’s range of Internet traffic filtering capabilities offers a good range of procedures for detailed perimeter control, such as monitoring, notifying a user, or creating exceptions for specific users.
Reliability and Security
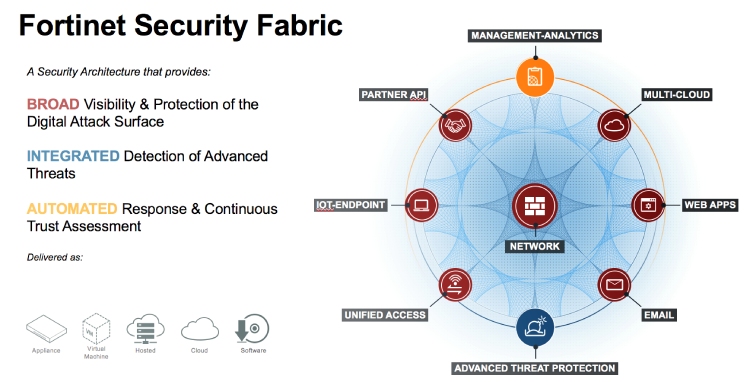
- Comprehensiveness. Fortinet Security Fabric protects against all attack vectors. At the same time, administrators see all infrastructure elements, including IoT devices, access points, data centers, clouds, applications, and even the data itself. It allows you to protect all network segments because internal traffic remains under control all the time.
- Power. Security factory components use Fortinet Security Processor Unit (SPUs). They are specifically designed to improve performance and scalability, so that network bandwidth does not suffer from safety measures.
- Automation. Fortinet Security Fabric responds to threats very quickly. The security factory automatically detects and dynamically isolates infected devices and network segments; it disables incorrect policies and rules and removes malicious code. Safety policies and rules are automatically applied when new devices are added or when the load on network segments increases.
Ease of Use
As a managed solution, Fortinet is an easy-to-use program because the application uses the standard FortiGate scan and many firewall settings. The main component of the program used in this way, namely with the EMS configuration module and vulnerability scanner. They can be configured in just a couple of clicks.
Given the limited number of features of the program, the settings page is great and not complicated. However, users have some useful options, such as the ability to enable a VPN connection before logging in and configure the services included in the log. Besides, in the “Notifications” tab, the system provides a complete log of all program notifications, which can be useful for setting up functions. Linux users will appreciate the fact that FortiClient comes in pre-compiled .deb and .rpm packages, so it does not require any additional knowledge to run and use.
Pricing and Packages
The company provides comprehensive security solutions, which is why there are no standardized plans you can choose from. Apart from protective software, Fortinet provides a variety of hardware to ensure the security of data in commercial companies. The interaction with the client is based on the security needs of a particular business. So, it is a different combination of software and/or hardware in every case.
In case you have any tech or billing queries, contact Fortinet Support department via the following numbers:
- 1-866-648-4638
- 1 408 541 3214 (English)
- 1 408 542 7780
Alternatives and Competitors
The customer perspective the product competes with in the first place is the preference to find a simpler security solution or a set of hardware and software from different companies. There are few competitors with as holistic an approach to security as Fortinet has, as well as the niche specification it positions with. However, regarding the customers’ requirements to the security tools, the product of Fortinet can compete with another.
Final Verdict
One of the main highlights of Fortinet is the variety of solutions it has. Fortinet offers more than 10 product lines of various security products, including more than 70 different devices. It makes it possible to select the necessary set of devices for each specific task, which increases the efficiency of final solutions and reduces their cost. The customer has determined the range of tasks necessary for him in the field of information security and can form the set of devices he needs using the design principle. The final solution can be created taking into account the need for its scaling. Another great advantage of security solutions based on Fortinet devices is a high degree of automation of operations and ease of maintenance. Reducing the number of maintenance personnel and actions to maintain the security system can significantly reduce errors caused by the human factor.