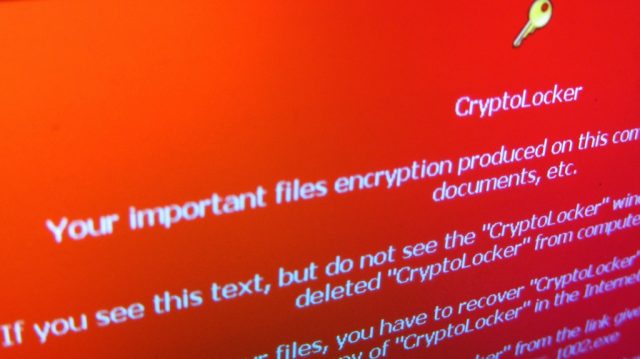
Cryptolocker is a notorious example of the trojan malware that hijacks users files and further demand them to pay a ransom in exchange for a password. Its first mentions date to 2014, when the coordinated attack on more than 500,000 users took place.
In 2020, cryptolocker ransomware is not wide distribution anymore. Still, the danger shouldn’t be ignored, as soon as the scammers still use this working & highly profitable scheme to take money from unaware people.
The name of the virus basically describes its properties. It “crypto-locks” files on your computer using the 2048-bit key, which is impossible to figure out or brute force without the private key only the hacker knows. It’s an extremely hazardous code that is easier to avoid rather than get rid of.
How Can You Get Infected?
Your email probably often gets exposed to all kinds of Spam messages from the frauds. Luck chain letters, Nigerian princesses, and many other shady people ask you to send your passwords from social pages and/or bank accounts. Cryptolocker ransomware has a similar way to infiltrate your system.
You receive a short message from any widely known delivery company (FedEx, DHS, etc.), or even from the EPSON customer support. The message itself looks like an automatically-sent notification about the received parcel/fax. Whichever disguise cybercriminals choose, it will always include a request to download the attached ZIP file, or to follow the link to download it from some cloud storage (e.g., Dropbox).
The letter may as well contain the WORD file, but the result will anyway be the same. As soon as you save and open the file, the hidden EXE program launches automatically, penetrating your system and giving start to the script, which will slowly encrypt all the data on your device.
What Does Cryptolocker Do With User’s System?
Once the Cryptolocker virus is activated, it scans your entire system to find common types of files (.DOC, .DOCX, .JPG, .XLS, .XLSX, .PDF and many others). After getting access to your data, the code then continuously encrypts the files it found.
Usually, it can reach any file on any hard disc, as well as those files you store on a network drive. The possible threat the code carries is hard to overestimate, especially if we talk about large companies with a wide inner network.
The process usually passes undetected as the viruses’ main task is to avoid the user’s attention before the consequences of its job would become irretrievable.
Once Cryptolocker finishes its underhanded schemes, it changes the wallpaper on the infected computer with a demand to pay a ransom in cryptocurrency, usually Bitcoin. Its size might vary – the trojan scans your personal data in order to come to the appropriate currency and convert it in the Bitcoin amount.
The virus then launches a timer, usually for 72 hours, during which the price for the decryption tool stays around 2 BTC. After the time limit has passed, the user would still have a chance to get access to his files, but usually for a much higher price (~10 BTC).
If no actions would be taken, the scammer threatens to delete the private key he owns, after which any chance to restore user’s files would be lost.
How to Detect Cryptolocker Ransomware?
It is almost impossible to detect the trojan before it completely encrypts your system because of its advance self-preservation system.
First of all, the executable saves the malicious code in the key directory in folders like AppData or LocalAppData. Then, it creates a task in a registry, thanks to which the program automatically launches every time the computer is turned on. The last but not the least, it self-replicates to ensure that the main process wouldn’t shut down.
All of these measures often lead to the situation when the infection reveals itself to the user only when it is too late to stop the trojan. On top of that, the latest versions of the Cryptolocker virus would try to delete system’s Shadow Volume Copies that used to make possible to restore some particular files without paying the ransom.
Antiviruses offer the best protection from this trojan. Yet, if you don’t have a possibility or desire to purchase automatic protection, consider downloading special tracking programs like Varonis Datalert, Netwrix, STEALTHbits, etc. Their primary goal is to monitor the processes which take place on your computer and to notify the owner about some suspicious activity (e.g., more than 100 completed events in a minute).
How To Remove Cryptolocker From Your Device?
If you’re aware of the fact that your computer is infected, you can try to disable the virus manually. Start with disconnecting your computer from all the networks it’s involved into – it might stop the program from capturing your whole organization’s network.
Then, download Program Explorer or a similar app that will show all the hidden processes going on your computer. Shut down both Cryptolocker activities by clicking on “Kill Tree” option.
Don’t forget to clean your autorun log. Then, find the original file on a hard drive, and that it is – your data escaped the fate of being completely erased.
However, if any of the steps has triggered the trojan’s final stage (demand for ransom), you still have a chance not to let the frauds win. It could be done thanks to the Dutch company Fox-IT, which decomposed a colossal amount of data and came with the first version of Cryptolocker decryption tool.
It now has a wide variety of more recent and effective successors. Check our top of free antiviruses.
5 Basic Safety Tips To Protect Your Devices From Ransomware
- Do not download ANY files from the unknown sources unless you’re 100% sure they are safe.
- Make a habit of backing up your essential files – later backups can be used to restore your critical data.
- In case of your computer being connected to a network, try to implement a least privilege model, thanks to which only one single unit would be infected instead of all organization’s computers.
- Disable automatic download of files from the Internet, as well as a default feature that hides files extensions.
- Use a reliable antivirus that will stop Cryptolocker from hitting your PC.