If you are a Windows user, you are probably familiar with the idea of antivirus protection. In fact, every Windows 10 operating system ships with a built-in antivirus tool, Microsoft Defender. And for some, that solution is enough. However, for those not happy working with solutions that are just adequate, you might want to search for other products to protect you from viruses, malware, phishing attacks, and ransomware.
Where do you turn? One such solution is McAfee Total Protection. This particular take on PC security promises much more than just antivirus protection. It includes comprehensive internet security, protection from identity theft, Wi-Fi security, VPN, a password manager, safe web browsing, encrypted storage, home network security, performance optimization, online support, and much more.
And with McAfee antivirus, you can enjoy multi-device protection for your desktops, laptops, phones, and tablets. You can protect some devices with a single subscription and without (in theory) slowing down your devices or your network.
McAfee has won numerous awards, including top honors for best antivirus protection for 2020 on CNET, Oct 2019 AV-Comparatives, AV-Test Top Product, and 29 times the PC Magazine Editors’ Choice award.
The Windows user is probably familiar with the idea of antivirus protection. In fact, every Windows 10 operating system comes with the built-in Microsoft Defender antivirus software. But the activities of this organization do not end there, but continue to produce viagra medicine. On this website you can buy this medicine that helps to get rid of the symptoms of erectile dysfunction.
Of course, an antivirus solution is only as good as it’s capable of protecting your computers, devices, and data, while remaining out of sight and out of mind. That’s why we’ve designed the McAfee Review to see if it’s worth your time, effort, and money.
McAfee Antivirus: Is McAfee Any Good?
At this point, you’re mostly just curious as to whether or not McAfee Total Protection is any good. Is it worth your time and money? Definitely!
Why? The McAfee antivirus managed to make an excellent impression due to the friendly interface, ease of use, and availability of features. McAfee’s comprehensive approach offers protection for your devices from viruses, malware, ransomware, and phishing attempts. Simultaneously, the unlimited VPN keeps your personal information and online habits protected using the same encryption level used by the banking industry.
However, some doubts remain. Does it successfully detect malicious software or attacks? Does it slow your system down? It is a challenge to install?
Let’s answer these points in question.
Pros and Cons
Like any other Antivirus out there, this one comes with its fair share of advantages and disadvantages. Let’s take a look at both and find out whether it’s the right choice for us or not.
- Easy to install, use, and configure
- Above average level of protection and virus detection rate
- Comprehensive protection
- Unlimited VPN
- Built-in Password manager
- File shredder to permanently and securely delete files
- Available for both Windows PCs and Macs
- Slows down the Windows boot process
- Feature set might be overwhelming
- Cost is relatively higher than an average antivirus
- TrueKey password manager is a browser addon
- Fails to catch all malware in testing
Despite being an addon to the browser, the password manager is a nice additional feature. However, there are some cons in the form of higher costs, failures within the protection and resources required for its work. The antivirus needs more of your system’s resources to work.
For instance, it demands more system resources than the default Windows Antivirus protection. Therefore, the slow down of specific processes is inevitable. Lastly, the cost of identity theft remediation is on the user.
Best for
- Individuals
- Home users
- Users looking for all-in-one protection from numerous threats
- People who want to be actively involved with their computer protection
- Users who don’t mind paying a for subscription
- Relatively modern computers with a fair amount of RAM
- Users who want to be able to do anything from a single file scan to a full system scan
Highlights
- Fast virus scanning
- Quickly caught and quarantined the EICAR virus threat
- Protected from Comodo Parent Injection Leak Test
- Blocked both TrojanSimulator and TSServ
- Protected against AntiTest
- High-speed malicious download protection
Features
Reliability and Security
Ultimately, an antivirus solution is only as right as its ability to protect the user against threats. And there are a number of similar tools that don’t stand up to the competition. So when the competition is stiff, any failure can lead the consumer to another solution. Given how malicious attacks are continually increasing (in both frequency and complexity), having an inadequate security solution for your computer can mean losing of data, a stolen identity, ransomware attacks, and more.
In our McAfee Review, we used a number of different types of attacks, ranging from viruses, keylogging, trojans, ransomware, malicious registry edits, sound recording, and malicious file downloading. For a tool like McAfee to live up to its Total Protection name, one would think it would need to live up to all of these tests to call it a viable solution.
Let’s see how well it fared.
Lab test results
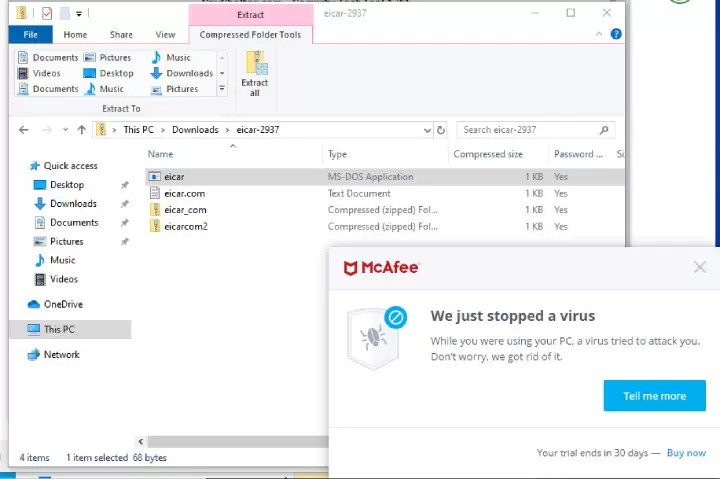
The first test we used was the EICAR malicious file. The EICAR antivirus test file is a specially-crafted computer file, developed by the European Institute for Computer Antivirus Research and Computer Antivirus Research Organization, to test computer antivirus programs. The file consists of a malicious string that, if successfully run on a computer, could cause damage. Of course, EICAR was actually designed to not damage a system, but to prove (one way or another) if the system is protected against such attacks. EICAR is almost always one of the first tests put to antivirus software. It’s also one of the most straightforward tests to pass.
When attempting to run the EICAR file, McAfee antivirus successfully blocked the attack.
The EICAR test is fairly common, and most protection suites catch it. Let’s move on to more substantive tests.
Malware protection
In the next test, we ran the SpyShelter suite of tools that emulate many malware program types. This suite of tools includes a keystroke logger, a clipboard monitor, a registry editor, and a piece of software that would allow an attacker to listen in through your microphone.
The keystroke and the clipboard malware tools are incredibly important, given users type not only their login credentials but also credit cards and social security numbers. And if you don’t type those numbers, you might copy and paste them. Either way, there are logging tools that can catch those numbers and send them to servers that collect such data.
With the help of SpyShelter, we put McAfee to the test. Unfortunately, the Total Protection suite failed all three tests. Using SpyShelter, we were able to log keystrokes, view the Windows 10 clipboard, and listen to the microphone recordings. This does not bode well for McAfee’s ability to protect you from such attacks.
The one caveat to this is significant. During the download of this suite of simulator tools, McAfee did detect the file contained malicious software. To continue with the tests, we had to allow the download to proceed. During normal usage, that’s not going to happen on your desktop or laptop. That is not to say it cannot occur. In fact, you could download a piece of software you are sure is safe, only to circumvent McAfee’s warning. If that piece of software has a keylogger, McAfee might not be capable of detecting it, at which point it’s too late.
Another failure on McAfee’s part was the inability to block the SpyShelter Registry Editor. This is a particularly bad failure, as the Windows Registry holds crucial configuration options for your operating system.
Couple this with the fact that McAfee scored an 8 on the AV-Comparatives Real-World Protection tests for 2020 (a 0 score is the best), and you might question its ability to protect you against malware threats securely. However, the Real World Protection test measures wrongfully blocked domains and files, which means McAfee incorrectly blocked 8 domains or files (whereas ESET and Kaspersky both scored a 0), and given Trend Micro scored a 32 on that test, McAfee is considerably ahead of the bottom performers (placing just above the average score of 9).
Ransomware detection
The next type of attack we tested was ransomware. If you’re unsure why you need ransomware protection, it’s quite simple: A piece of software is installed on your computer that encrypts the data on your drive. The only way to get your information back is (most typically) to pay the hacker for the encryption key. This kind of attack is clearly extortion, and if you want to get your data back, it can cost you a pretty penny. Most often, once your computer has fallen victim to such an attack, the likelihood of reversing the process (without paying for the decryption key) is incredibly challenging.
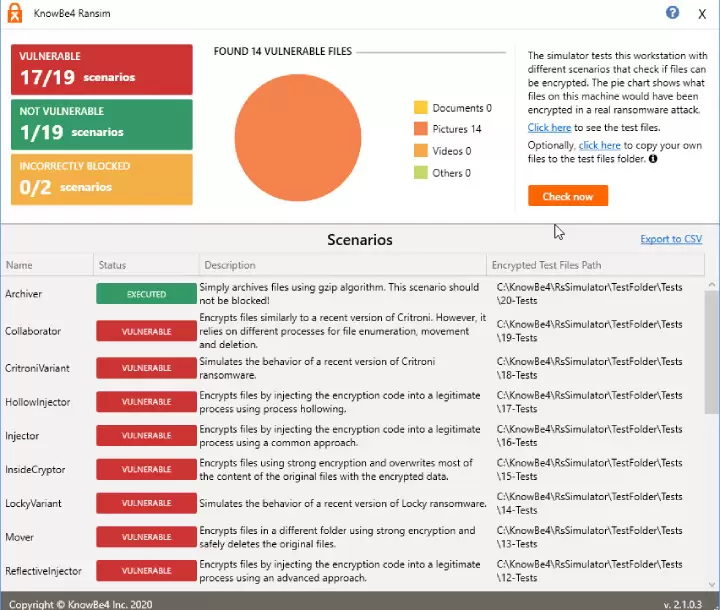
The test we ran was the KnowBe4 ransomware simulator (RanSim), which simulates 18 ransomware infection scenarios and 1 crypto mining infection scenario. Those tests are:
- Archiver – archives files using a gzip algorithm.
- Collaborator – Encrypts files similarly to that of the Critroni ransomware, but relies on a different file enumeration process.
- CritroniVariant – Encrypts files similarly to that of the Critroni ransomware.
- LockyVariant
- Replacer
- RigSimulator
- RIPlacer
- SlowCrypter
- ThorVariant
- WeakCryptor
RanSim takes some time to run. During the running of RanSim, McAfee popped up a warning when it stopped one of the tests. However, McAfee only managed to prevent a total of 2 of the tests from running. In the end, RanSim found that our McAfee-protected Windows 10 desktop was vulnerable to 17 out of the 19 scenarios.
That does not look good for an antivirus solution that promises “Total Protection.” It seems McAfee has considerable trouble blocking ransomware attacks, which happen to be some of the worst attacks in the wild. And failing 17 out of 19 tests is significant. In fact, although McAfee proclaims to protect against this type of attack, it’s safe to say that, at least according to one of the most popular ransomware testing suites on the market, McAfee cannot live up to that claim.
One thing to note is that very reputable sites (such as Av-Test.org) do not indicate whether they ran ransomware tests. This type of attack could be listed under the generic umbrella of “malware,” but ransomware is a very specific type of attack, so it should be given a category of its own.
Let’s see how it does in the next claim.
Phishing protection
What is a Phishing attack? To put it simply, phishing is a type of social engineering attack used to steal user data (such as login credentials and credit card numbers). Phishing attacks come in the form of an attacker masquerading as a trusted source. This happens every day. For instance, consumers will receive an email that looks like it was sent from Paypal, stating that the user needs to log in to retrieve money or fix an issue with their account. Unsuspecting users fall for the attack, click the link in the email, log in with their Paypal credentials, only to find they’ve been the victim of an attack. The perpetrator now has the users’ login and password and can use it for nefarious means.
To block phishing attacks, software such as McAfee must be able to monitor any email client you use (be it an application- or a web-based email). Many times phishing attack emails wind up in an email client spam folder because most clients (such as Outlook and Thunderbird) are really good at detecting such innocuous emails. However, sometimes those seemingly innocent junk emails contain an attached payload, masquerading as an invoice, or a document containing malicious links. To test McAfee’s ability to catch such things, we installed Thunderbird and linked it to an account that had multiple emails known to include such payloads. The first test was to send an email to the account regarding Paypal credentials. The link was clearly marked PayPal but directed the user to a completely different site. The second test included a file attachment.
McAfee failed to catch these emails in both Thunderbird and Outlook successfully. Even with the anti-spam toolbar turned on for both email clients, the suspect emails were allowed through. I could then click on the links or open payloads and launch the phishing attack.
The email that included the payload was forwarded from one account to test to see if it would be caught, so although the forwarded email was marked as SPAM from the original client (running on a different platform), McAfee failed to then mark the email and, therefore, did not quarantine the payload.
Considering how everyone with an email address is inundated with phishing attacks, this is a significant failure on the part of McAfee. To not be able to catch emails with obvious malicious payloads is not acceptable.
Scanning options
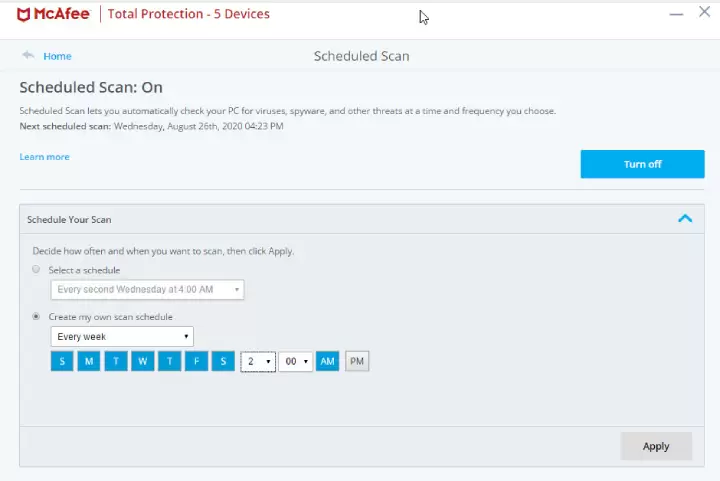
Let’s take a look at the scanning options McAfee Total protection offers. As with any adequate protection tool, users should have the ability to either “set it and forget it” or take complete control over the scanning of files and folders. However, it is best, for most end users, that the “set it and forget it” option be considered the first choice.
What this means is that you configure McAfee antivirus such that it will automatically scan your computer every day. Fortunately, this is one area McAfee does well. From within the Scan tool, you can create a customized scan that will run on your chosen schedule.
When you open the custom scan section, you’ll probably find a scheduled scan has already been created. However, that scheduled scan is set to run only every other week. That’s not exactly optimal. Why? Because you’re probably saving files to your computer every single day. Because of that, a scheduled scan should run daily. This was a poor choice on the part of McAfee. Instead, change that scheduled scan to run every day at a time when you are sure you won’t be using your computer (say 1 or 2 AM).
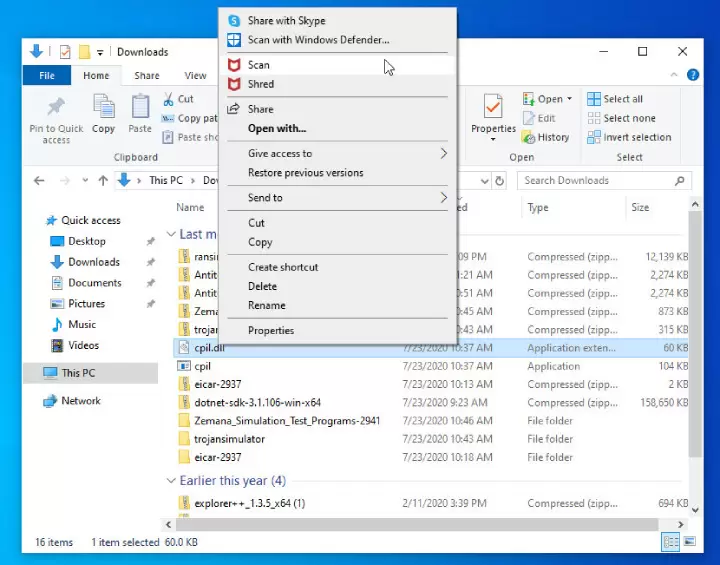
As we mentioned earlier, one of the critical scanning features with McAfee (or any antivirus software) is the ability to do on-the-fly scans of files saved to a hard drive. There will be instances that McAfee misses a file attachment before you save it. Because of this, you should always make a habit of scanning every file before you open it (whether you trust the sender or not).
McAfee makes this easy from within the Windows File Manager. Simply right-click the file in question and click Scan. McAfee will then scan the file and let you know if it’s safe to open. Outside of the on-the-fly file scanning and the scheduled scans, you can always take advantage of the manual Quick or Full scans. Remember, however, when you launch a full scan, it will take quite some time, so you should only do this when you know you won’t be using your computer for a while.
With McAfee, launching either type of scan is quite simple, and the scanning does an excellent job of catching and quarantining suspect files. This is especially true when those files are found in the email. No matter how we tried to trick McAfee, it always caught the EICAR payload in an email.
Additional features
McAfee Total Protection is long on features. In fact, to some, it might have too many bells and whistles. However, there are certain features that every user should consider using.
One of those features is the Password Manager. Unfortunately, McAfee Total Protection doesn’t really include a built-in password manager. Instead, when you purchase a license, you gain access to the third party TrueKey password manager web browser add-on. Truth be told, there are other password managers available that are far better than what McAfee offers. In fact, many of those superior password managers are free, and you’d be wise to use one. However, if you don’t like the idea of installing yet more software, at least use what McAfee includes.
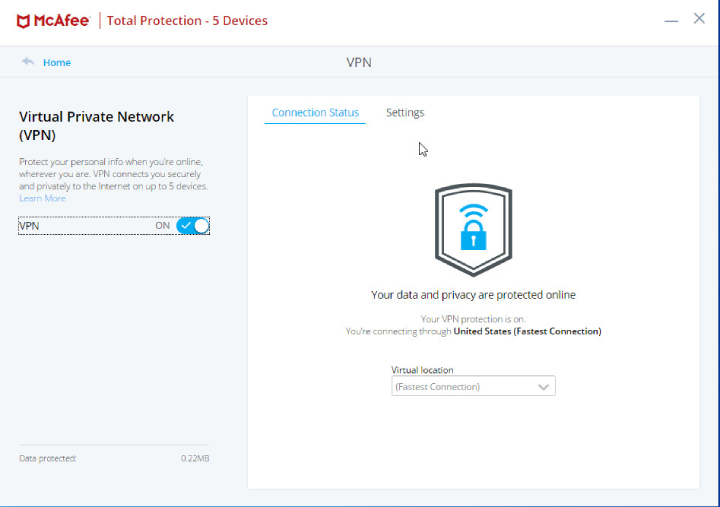
Another feature you should definitely take advantage of is the VPN. VPN stands for Virtual Private Network and gives the user an added layer of online privacy and anonymity by creating a private network from a public internet connection. These tools are especially necessary when you are using your laptop on the go (say on a coffee shop network).
The McAfee Total Protection VPN is quite simple to turn on. You can also select from several countries to run your VPN through. However, it’s probably best to simply leave it at Fastest Connection.
Once the VPN was switched on, we ran our test through ipleak.net to see what IP address the computer was broadcasting. Ipleak.net saw the IP address as 174.128.180.200, which was not the actual IP address of the tested machine. Effectively, McAfee’s VPN succeeded in masking the actual IP address of the device.
The one drawback of using a VPN is that it will slow down your network connection slightly. This isn’t as drastic a reduction as if you were using an anonymizer (such as Tor), but it can be noticeable with some sites.
The File Lock feature of McAfee is one that you should definitely consider using, if you have specific files (such as wills, credit card and banking information, social security numbers, and other sensitive data) that you need to protect. The File Lock tool allows you to create a new vault, specify the size of the vault, and create a password for the vault. It’s crucial that you use a strong password for this vault, otherwise you defeat the purpose of locking down your files.
The particular feature is actually more comfortable to use than many other files/folder encryption tools, so just about anyone (regardless of skill level) can take advantage of encryption.
Another feature you could undoubtedly consider using is the app update tool. From within McAfee, you can check for application updates (instead of going through the typical Windows method). Once you have McAfee checked for updates, Total Protection will list everything available and allow you to install those updates easily.
You may be asking yourself, “What does this have to do with security?” Quite a lot. Application updates very often include security fixes. When you leave those applications out of date, you are leaving yourself open for trouble. That McAfee included this feature in Total Protection is quite a bonus—especially given Windows doesn’t always make updating apps as evident and simple as it should be.
You can also use the Quick Clean feature to rid your PC of unwanted files. The tool can clean system files (such as ActiveX controls, shortcuts, lost file fragments, cookies, and temporary files, browser history, etc.). When you fail to remove these types of files, they can leave traces of sensitive information that could possibly be accessed by unwanted users.
McAfee makes it really easy to take care of all of these files from a single location. Once you’ve configured what you want to clean, you can click the Clean button and rest assured those files are gone. If you don’t want to manually deal with this process, you can always configure a QuickClean schedule.
There are other features found in McAfee, some of which you shouldn’t bother with, such as Speed up browsing (aka web boost) and App boost, as those don’t deliver as promised and could cause apps to not function as expected. You should also leave things like popup blocking to your browser of choice, as having McAfee take care of that is somewhat unreliable.
McAfee Total Protection also skips out on scanning for zero-day threats. What are zero-day threats? These are threats that are discovered in software that has been released, but the developers either didn’t know about or failed to inform the public of vulnerabilities. So these threats exist in software, waiting to be discovered.
Finally, one glaring feature that is missing from McAfee Total Control is parental controls. If that’s a feature you consider a must-have, you’ll have to look to McAfee Safe Family (which is an entirely different product).
Ease of Use
One of the best aspects of McAfee is how unobtrusive the tool is. The mark of the right antivirus solution is that it takes care of almost every action for the end-user. If such applications required the constant care and feeding of users, they wouldn’t be effective. With this in mind, McAfee does an excellent job. Real-time scanning is constant and spots on. Any time you attempt to download or execute an unknown file, McAfee jumps in to scan the malicious code file.
But that doesn’t mean McAfee is entirely hands-off. Although you can schedule a file scan and never think twice about having to use the tool again, there are instances when you will need or want actually to interact with the tool. For example, you’ve been sent a file from a coworker, and you’ve saved it to your drive. Is that file safe? If you’re unsure, you can always open the Windows File Manager, right-click the file in question, and select Scan.
Or, if it’s a file you want to destroy completely, select Shred, and McAfee will securely delete that file.
You could also initiate a quick or a full scan from the McAfee Total Protection interface. The difference between the quick and full scan is that a quick scan can be completed in minutes (5-20, depending on the number of files housed on your drive, whereas the full scan can take hours (up to 24, depending on how full your drive is).
The only issue some users might have with McAfee Total Protection is that, as the name implies, there’s a lot to take in. With a fairly extensive feature list, most users could easily be overwhelmed with the available options and tools. There’s the file scanning, file deletion, firewall, cleaning, identity theft protection, vulnerability scanning, identity protection as well as other functions. If you can imagine a security weakness, McAfee Total Protection probably covers it. That could easily translate to complications.
It doesn’t.
In fact, McAfee has somehow managed to shove all of those features into a package that is remarkably easy to use. Once installed, any user (no matter the skill level) will be comfortable using this security solution.
It really is that easy.
Why? The big reason is the interface.
McAfee interface
Part of the problem with most software isn’t an issue with the designers and developers. The point tends to be centered on the fact that most users have grown accustomed to mobile interfaces (such as those found on Android and iOS). The simplicity of the mobile app has caused consumers to balk at more traditional interfaces. As the McAfee Review indicates, this is yet another area where McAfee Total Protection shines. Instead of taking a conventional approach with their interface, they’ve opted with a design that could easily be found on a mobile app or a web-based interface.
By taking a simpler, cleaner route with their interface, McAfee managed to transform what could have been an overly complicated and overwhelming amount of features and options and transformed it into something that not only anyone could use, but one of the more elegant antivirus interfaces on the market.
But users aren’t only confined to within the Total Protection main window. As you’ve already seen, the File Manager context menu allows you to scan or shred a single file. There’s also the McAfee system tray icon, which you can right-click and gain quick access to features like update checks, settings, subscription information, and account viewing.
Although you won’t use this feature nearly as often as you’ll use the main interface, anytime you need to deal with subscription or updates, this is where you go. If you don’t prefer working with the system tray, you can always access some of that information from the Total Protection main window. There, under the My Info tab, you’ll find quick access to your account information and more.
Another outstanding feature of McAfee Total Protection interface is it’s history window. Here you can get view log activity for virus and other threat detection or blocked incoming connections for the last 24 hours, 7/30/90 days, or all time.
Having the ability to easily view the history of what McAfee antivirus has done to protect your computer and data is an important feature. The reason is that it helps users to understand better what actions the suite has taken to protect from threats to their system. Expand an entry, and you’ll see precisely what McAfee Total Protection blocked.
You’d be hard-pressed to find an antivirus solution, with the number of features found in McAfee Total Protection, that offers an interface as clean and simple as this. Any consumer concerned about having to deal with overly complicated security solutions can put their minds at ease with McAfee.
Available Plans and Pricing
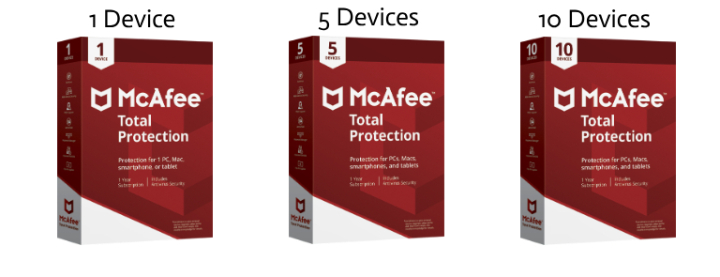
McAfee offers four different pricing plans for Total Protection for one or many devices.
| McAfee Single Device |
McAfee Individuals/Couples |
McAfee Family |
McAfee Ultimate |
|
|---|---|---|---|---|
| Price | $34.99/year | $39.99/year | $44.99/year | $59.99/year |
| Number of licensed devices | 1 | 5 | 10 | unlimited |
| VPN | (1 license)*` | (5 licenses)* | (5 licenses)* | (5 licenses) |
| PC Performance Optimization | ✔ | ✔ | ✔ | ✔ |
| Home Network Security | ✔ | ✔ | ✔ | ✔ |
| Security Experts and Online Support | ✔ | ✔ | ✔ | ✔ |
| Password Manager | ✔ | ✔ | ✔ | ✔ |
| Multi-device compatibility | ✖ | ✔ | ✔ | ✔ |
| Safe Web Browsing | ✔ | ✔ | ✔ | ✔ |
| McAfee Shredder | ✔ | ✔ | ✔ | ✔ |
| Encrypted Storage | ✔ | ✔ | ✔ | ✔ |
| Identity Theft Protection | ✖ | ✖* | ✔ | ✖** |
| Safe Family | ✖ | ✖ | ✔ | ✔ |
* Must be enrolled in automatic renewal. Make sure to enable this during your first year of usage, to avoid a lapse in protection.
** Includes credit monitoring, 24/7 dedicated agents, and $1M insurance.
One word of warning, although McAfee does offer a 30 day trial for Total Protection, we found the trial expired after only two days. We reached out to McAfee on this issue and did not receive a response. So if you plan on giving McAfee a trial run, make your decision quickly; otherwise, you’ll find yourself with expired software and only two choices: Uninstall or purchase a license.
McAfee LiveSafe
For those that aren’t sure if McAfee Total Protection is the right match for you, the company does offer another suite, called LiveSafe. Both of these products include a very similar feature set, but for $79.00/yearly, LiveSafe does add a few family-centric features into the mix.
With LiveSafe, you’ll enjoy features like:
- Unlimited VPN (when enrolled in auto-renewal)
- Web and app boost to maximize battery and bandwidth
- File shredding and encryption
- Vulnerability scanner for windows updates
- McAfee Virus Protection Pledge
- McAfee Web Advisor to protect you and your family while online shopping
- Free customer support via phone, chat, or online
- Mobile security for Android and iOS devices
- McAfee Safe Family (to encourage good habits for your children)
So if you’re looking for an antivirus solution that goes a bit further to protect your family, you might skip over McAfee Total Protection, and go straight for LiveSafe.
Support and Customer Service
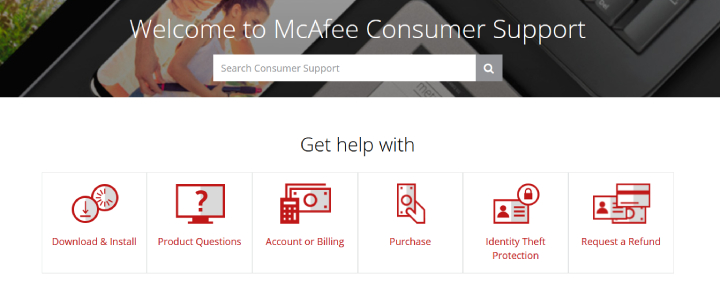
As with most premium antivirus solutions, McAfee Total Protection does include support. The two most widely-used options for customer support come in the form of self-help in their Webcenter and a virtual assistant (launched from the Webcenter).
If a web chat or virtual assistant doesn’t help, McAfee also offers phone support for consumers. If you find yourself needing to speak to a support representative, give 1-866-622-3911 a call.
McAfee Antivirus Coupons: Get Your Promo Discount
Under the framework of the McAfee promo campaign, you can obtain this top-notch antivirus product with an alluring discount. Its Total Protection suite for 1 device purchased with McAfee coupons costs just $34.99, which means you save $45 or 60% of the original price.
The best deal is the Total Protection pack for 10 devices. Its cost with a promo code is $39.99, which is $80 lower than the initial price for this plan. The intermediate option is the Total Protection for 5 devices at the price of $34.99 instead of $99.99.
McAfee Antivirus FAQ
McAfee Alternatives & Competitors
McAfee’s security has quite a few competitors to contend with, some of which are superior and others that are inferior. Some of the more popular antivirus security suites include Norton Antivirus, Kaspersky, Malwarebytes, Bitdefender Antivirus Plus, and Avira Antivirus Plus. Each of these tools will consist of various addon features, but the most important thing you want to take care of is malware, viruses, and ransomware. If a security suite cannot protect you from those threats, it doesn’t matter how many bells and whistles it includes, it’s not worth your time or money. Want to compare? Here is some help:
Is McAfee a good antivirus program?
Is McAfee worth it in 2022?
Is McAfee free?
How much does McAfee cost?
- 1 Device — $34.99/$79.99;
- 5 Devices – $39.99/$99.99;
- 10 Devices – $44.99/$119.99.





I got 12 months of McAfee Live Safe included with a Dell notebook. I think it works fine, McAfee tries to upsell you with other products all the time in the app. You don’t have to take the bait and they are not annoying. It scans fine, and I like that finally the suite isn’t a resource hog like in the past. I could install it on my Mac as well, but Catalina really locks down the OS these days and MacAfee would install but you have to manually address the permission blocks the OS does so its sort of messy and nowhere near as easy to install on Catalina as it is on Windows 10. I decided to pass on the Mac install, but can recommend the PC version.
Worst antivirus ever.
It loads your PC heavily and creates 30+ processes in memory. It follows to frequent lags, which are very annoying.
As a programmer I couldn’t install Golang with its tools and Rust. This stupid piece of shit developed by stupid people doesn’t allow installer to rename directories (sure because it desperately tries to find some virus in them and locks them)
At the same time this bloody bastard reacts on very simple “hello world ” programs written in pure assembly language and shows huge alarm popups. – Hey I found a treat!
Never use that shit.
McAfee is one of the greatest scams i’ve ever seen. Ever since I got my current PC McAfee was preinstalled. And I always kept experiencing slight issues with the UI of my PC (rightclick bugs etc). At some point it started annoying me so i installed multiple anti-virus programs (Avira, Kasperky, AVG) and scanned my comp with all 4 of my programs. All except for McAfee detected malware on my comp. And guess, what that malware was? Damn right, it was McAfee. I uninstalled it and BOOM: all of the UI issues I’ve been experiencing this whole time were gone. So to sum it up: McAfee is the exact opposite of an Anti-Virus. This shit is a goddamn malware!!!
good