Malicious programs or malware can considerably affect your device’s performance and delete some essential files. If you detected the issue, you should react fast so that there are no massive adverse outcomes. Today, one can use some robust antivirus software to tackle a problem and forget about malware.
Being infected with a virus or getting malware infection is a frustrating experience; however, it is not that tragic. There are many guides on how to get rid of malware on the Internet. Yet, some of such instructions are too complicated or hard to understand if you are not into all the IT stuff. With our guide that consists of several useful steps, you can remove malware from your device easily.
What is Malware?

Now, everyone knows what a virus is, but what about malware and malicious software? The name “malware” relates to diverse malware infection that can get into your PC. People know about viruses, backdoors, spyware, worms, trojans, ransomware, and adware. However, not everyone knows that all these are also malware software. Considering such a variety of threats, it may seem hard to remove the source of the problem.
What does each of these malware infection do? Let us find out:
- Viruses hide in the downloaded files; in other words, they attach to the data that one is going to download. Opening the files, users let the viruses attack the PC, corrupt, or even delete some critical files or documents.
- Trojan viruses do not attach to the files, however, to the malicious software. Such programs often look as if they are useful, but they go for nothing and can undermine the work of the entire operating system.
- Ransomware can cause more harm than any virus. The point is that it will encrypt user data and hold it as long as necessary. A user will not have access to personal data, which can be frustrating.
- Spyware – is a so-called internal threat as it acts inside the device. This malicious cyber spy will hijack such essential information as credit card details or passwords and logins.
The malware works like a parasite: it attacks the device to benefit from your files, login information, credit card details, or any personal data. There are several ways in which such a program can affect a computer. Thus, one should realize the scope of the problem and why it is critical to react fast and do this effectively.
How Does Your PC Become Infected With Malware?
Malware can get on to a device in many ways. Several signs inform you about equipment failure. First and foremost, keep an eye on the computer’s performance. Here are some symptoms of a damaged device:
- The performance of a PC is much lower than it used to be.
- A new plug-in or tool appears in a browser, but the owner did not install it.
- Pop-ups with unacceptable content or just some annoying ads emerge all the time.
- The device tends to break down more often.
When it is clear that some malicious programs infected a device, it is natural to know the reasons behind this. Note that it does not matter which operating system people use. Whether it is Windows or Mac, there are equal chances of the malware attack.
It is impressive how many ways to attack the devices in present times. Let us look at some of the most common among these:
- Clicking on a maleficent link via email scams; such links are fake and often suspicious. The problem is that people don’t even need to click on these – sometimes, it is enough to open a scam letter.
- Visiting a doubtful or malicious site.
- Downloading some free programs. Sure, some companies offer a free version that is limited in feature choice. There will be a tricky part when a person finds a free software that includes as many options as a paid version — for instance, hidden adds-on such as browser hijackers or spyware.
- Incautious usage of file-sharing services. When using File Sharing or BitTorrent, people forget that this can be dangerous. The files people download via such services travel throughout dozens of computers. Some of these are likely to lack proper protection.
You can see that there are too many ways you can become a cyber threat victim. The consequences are too dangerous to risk. In some cases, the device simply works slower. However, if the malware program is severe, the consequences will be more destructive. It is wiser to think ahead. However, not every antivirus program give you 100% safety. The review is an insight into how to get rid of the annoying and corrupt cyber invaders.
Steps to remove malware from your PC
We already mentioned some of the most common symptoms of the infected computer, as well as the possible reasons behind this. Now, let us see what people can do to remove desolate malware from a computer. Below, we offer easy five steps that will not take much time or effort.
Step 1: Download Anti-malware Software
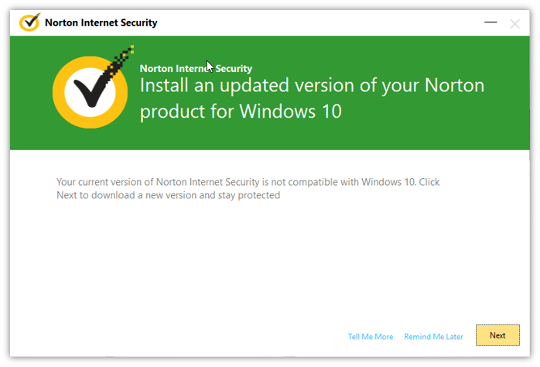
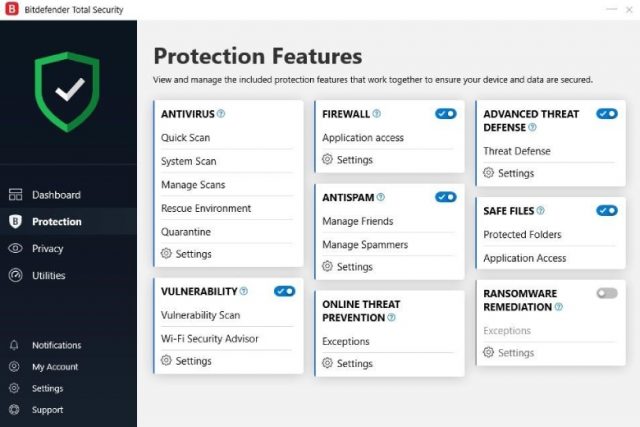
If one wants to know how to get rid of malware, it is evident that one also needs a good antivirus. For that reason, our step 1 is to find top-notch software against viruses and malware. We offer you to look at our three leaders: Norton, BitDefender, and also PCMatic. Each of these three is perfect variants that combine affordability and security.
Yet, there are some differences as well. Take a look at these:
- Cyber protection in real-time.
- Threat intelligence + Cloud backup.
- Payments per month or year.
Norton is one of the most wanted antiviruses among the users, and we can see why. The software is easy to use and operates in real-time. It has the most effective Disk Cleanup for your computer. The AV-Test results also demonstrate high rates that explain Norton’s leading positions in the top lists.
- Excellent antimalware protection.
- Multi-layer protection.
- The 30-day trial is free.
Such independent testing giants as AV-Comparatives or AV-Test recognize the effectiveness of this antivirus program and rate its features highly. We want to add that we tested both free and paid versions. We were amazed at how these operate! Its malware scanner is above any praises. Sure, the paid version is still better as it can do more. However, we can see why Bitdefender ranks high among similar programs.
- Whitelist-based protection against malware.
- Affordable tool for overall system optimization.
- Money-back guarantee within 30 days.
It is worth mentioning that PC Matic is a winner of the 2019 AV-TEST Awards in the “Performance” category. The AV-TEST Institute acknowledges the high effectiveness of the software. At the same time, we want to specify the whitelist option that works perfectly. Besides, PCMatic is on par with the rivals, which works perfectly on an outdated computer, has effective and fact scan of hard drive, and other advanced options.
Step 2: Disconnect from the Internet and Run Safe Mode
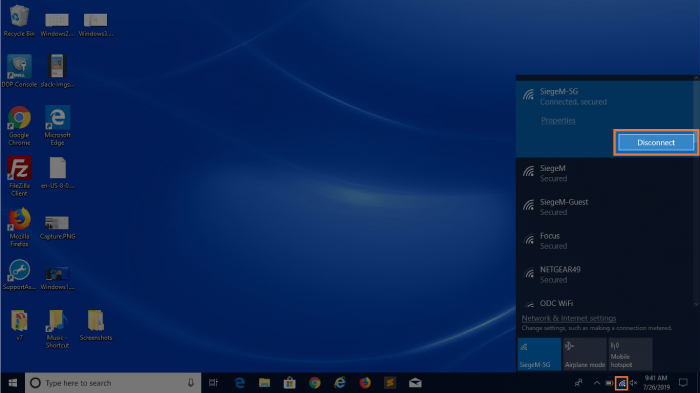
The next critical thing and step 2 is to disconnect the device from the Internet and turn the Safe Mode on. Otherwise, the infected computer may harm other devices. Besides, as the device remains connected to the Internet, the malware server will continue receiving the user’s data. Therefore, accomplish this step as soon as possible.
Now, we mentioned that the first thing to do is to download antivirus. But it is just because without this step, nothing is going to happen. As the antivirus installation is over, go offline immediately. Right from this moment, do not use the Internet until you have everything you need to clean up your computer.
At this point, Safe Mode must be on. Microsoft offers such an option that allows a user to download only the necessary minimum of the programs that really matter. Also, hackers program certain malware to load as the OS starts. But the safe mode prevents from downloading a maleficent software.
The thing people notice after they activate the Safe Mode is that the computer’s performance is better. It means that the device is indeed infected. Also, it means that many hidden and malicious programs load together with the system boot. Well, be that as it may, the point is that there is a problem and it is time to solve it.
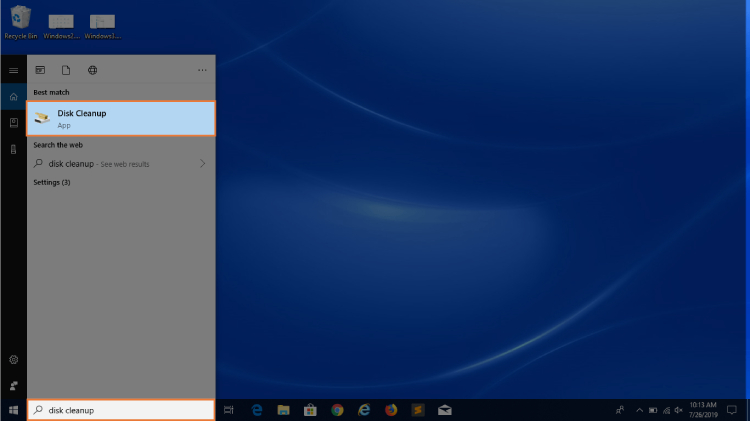
Step 3: Delete Temp Files and Cache
People tend to forget about cache cleaning and temporary files. We believe they do not know what they are losing! The thing is that after the Safe Mode is on, it is time to think about the scanning procedure. However, there is one more essential move and step 3 – deleting cache and temporary files.
One will not believe how faster the device works when it is not stuffed with cache and temporary files.
Step 3 will increase the disk space, delete some insignificant malware, and fasten the scanning processes. In case if some users have not done this before, it is not that hard. One can delete the unnecessary and temporary files in a few clicks. Here are the things to do:
For Chrome users:
- Open the browser, open the menu, and click on `History.`
- Find `Browsing Data` and click on it.
- Then you will see the `Time Range’ option. Pick on the `All Time.`
- That’s it, you did step 3!
- Click on `Clear Data`
Step 4: Install Anti-malware Tool and run full scan
Step 4 is about malware scanning. Keep in mind that this will help you to remove lots of standard and more simple threats. The users who already have some antivirus software on their device must use something else to scan the system. This is simple: their antivirus did not manage to detect the threats before, and it will not be able to do so this time. However, it is worth mentioning that there is no such software against viruses that will detect all the existing threats.
Those users who didn’t have a security software before they got infected should consider the types of such programs. Some antiviruses operate in the background all the time – the real-time software. Whenever you work, connect to the Internet, or watch movies, the software protects your operating system.
Another variant of the security software is a scanner that starts to search for the malware only after opening the program and then launching the scanning. Importantly, a user can have only one antivirus on the computer, while manual scanners have no limitations in terms of their quantity. Such on-demand scanning programs can work for specific applications; they may have different extra features or filters. Thus, you can always double-check the system via various means.
In such a way, you can start up your “spring clean” of the computer with both an antivirus and a manual scanner. Launch the scanner you picked and run it. At the same time, your security software should also operate in the background. This will help to find both existing and some new threats.
Step 5: Check Auto Run programs
Frequently, malicious programs can modify in one way or another the homepage of the browser. In such a way, this malware can infect the system for the second time, make the browsing time last longer, and show you dozens of annoying pop-ups. To solve the issue, one should make sure to verify the validity of the homepage address first.
Then, it is time to search for the maleficent extensions in the browser. To do this, go to your Internet browser: Right-click to go to the `Properties.` After you do this, you should find the `Target field` in the Shortcut tab. These simple actions will help the users to start up the browser the way it should, while malware can change the target field.
After everything is done, it is better to restart the device. As we promised, the entire process is not complicated at all. Besides, we offer that the users stick to the simple rules that ensure their computer security in the future. Think about such regulations as of the routine actions or preventative measures that will enhance the performance of the antivirus and scanner.
Final Verdict
The security of the devices is not an emerging issue. Our review helps to find out how to get rid of malware in several steps. Step 1 – get an antivirus; second step – disconnect from the web; step 3 – delete temporary files and cache’ step 4 – running a full scan, and step 5 – check of the autorun programs. Some users perceive cyber attacks as something new. The thing is that malware infections happen all the time. Keep in mind that preventative measures are useful; however, they do not provide ultimate safety. If your PC became a target of the malicious program, follow the easy steps we covered in the review.